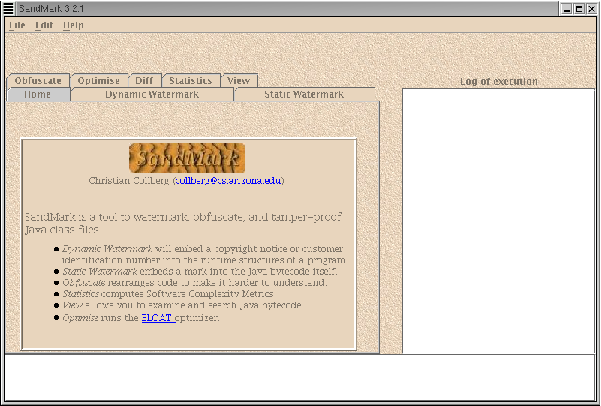

SandMark is a tool developed at the University of Arizona for software watermarking, tamper-proofing, and code obfuscation of Java bytecode. The ultimate goal of the project is to implement and study the effectiveness of all known software protection algorithms. Currently, the tool incorporates several dynamic and static watermarking algorithms (such as those proposed by Venkatesan, Collberg, Stern, and others), a large collection of obfuscation algorithms, a code optimizer, and tools for viewing and analyzing Java bytecode.
SandMark is designed to be simple to use. A graphical user interface allows novices to easily try out watermarking and obfuscation algorithms. Algorithms can be combined, the resulting watermarked and/or obfuscated code can be examined, and attacks can be easily launched. SandMark has been designed using a plugin-style architecture which makes it easy to extend with additional algorithms.
We are currently using SandMark to study which software watermarking algorithms are vulnerable to which code optimizations and code obfuscations. We are also interested in evaluating the effectiveness and performance overhead of obfuscation algorithms.
The development of SandMark is supported by the NSF under grant CCR-0073483, the AFRL under contract F33615-02-C-1146, and by the New Economy Research Fund of New Zealand under contracts UOAX9906 and UOAX0214.
| Note: This is an early, experimental, version of SandMark. It is stable enough to play with but should not be relied on for production use. It is known to work under Linux but not under Windows. Future versions will fix this. |
The following people have contributed to SandMark:
| Christian Collberg | Gregg Townsend, | Edward Carter |
| Balamurugan Chirtsabesan | Kelly Heffner | Andrew Huntwork |
| Kamlesh Kantilal | Andrew Lenards | Danny Mandel |
| Ginger Myles | Jasvir Nagra | Rathna Prabhu Rajendran |
| Ashok P. Ramasamy Venkatraj | Tapas Sahoo | Anna Segurson |
| Abin Shahab | Siwei Shen | Martin Stepp |
| Mike Stepp | Clark Thomborson | Xiangyu Zhang |
| Michael Chin | Sean Devine | Justin Cappos |
| David Leventhal | Steven Kobes |
For more information on software watermarking, tamper-proofing and code obfuscation, see